By A Mystery Man Writer


16 Real Examples of Business Email Compromise (BEC) Attacks

Gone Phishing: How Phishing Leads to Hacked Accounts and Identity Theft - Nouvelles de sécurité - Trend Micro FR

phishing website detector. (user's identity)pptx

What is Phishing? Detect & Prevent Phishing Attacks
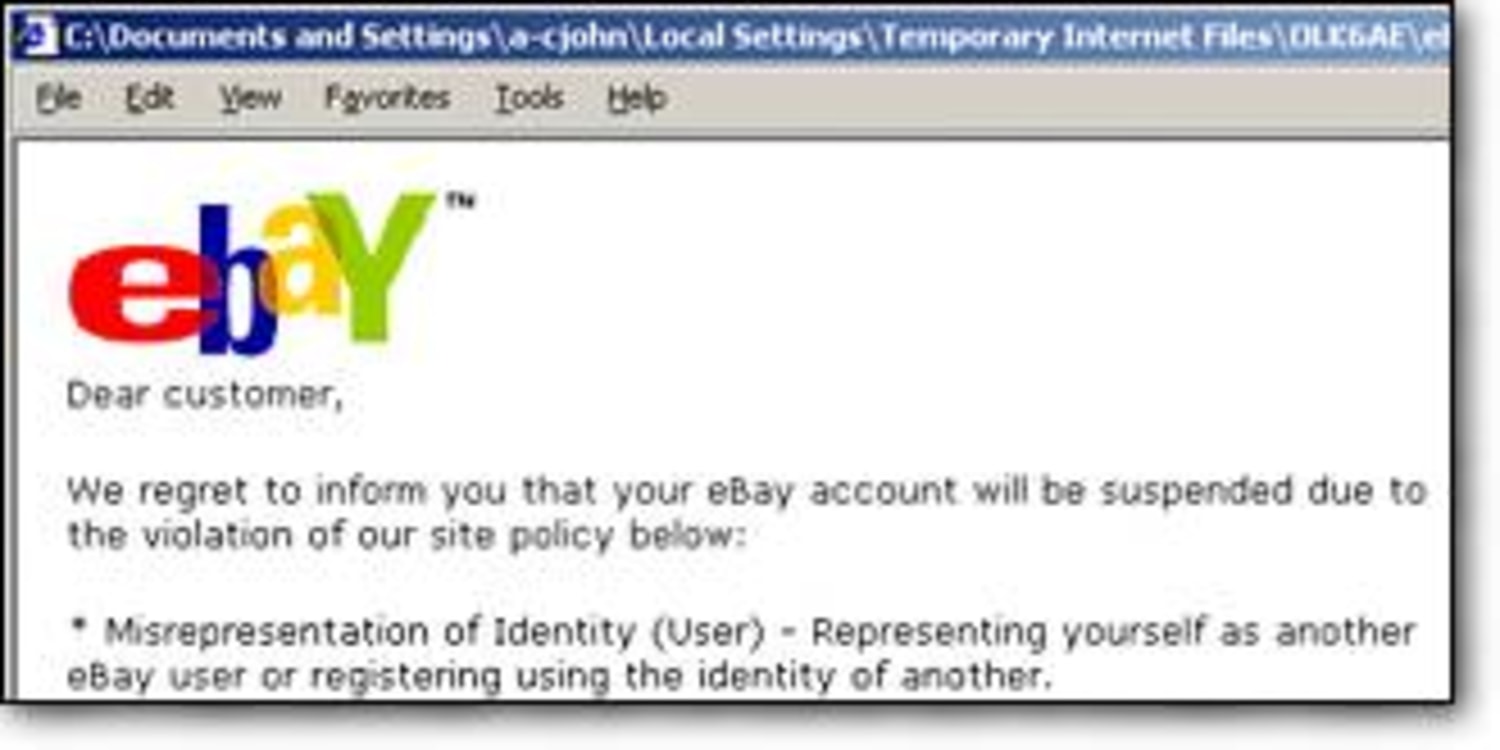
Look-alike e-mail scams on the rise

Social Engineering: Definition & 5 Attack Types
Gone Phishing: A Guide to Identifying Facebook Email Scams
What Is Phishing And How It Affects A Business

Phishing - Wikipedia